LAB 000 – Starting by Choice
Happy Friday! Mu, I promised you way back when (circa 2015) that I’d start a blog about networking and infrastructures, while trying to help and educate during the process… I guess this is the unofficial start of it. I know, I know… The idea was hatched many MANY keystrokes, client build outs, and exams attempts ago. So I wanted to kick the festivities off with two quick things. First, with an announcement from Cisco regarding the current CCIE Lab Exams. I’m not entirely sure how many people will be directly effected, however I know at least one NC Native as well as a bunch of people in the Sec V5.0 Lab Study Groups that are happy about things like this. At any rate, Cisco has extended the current version of the CCIE Lab exams for an additional few weeks. Secondly, I’d also like to give away something… To anyone who may be able to use it. So, if you were like me for most of last year, you were late night labbing with two very special women {Lady ISE and EVE} while stuffing as much knowledge about network security into your head as humanly possible. I’d like to release one of the full scale labs I created from scratch to study with for general consumption. (link at bottom of the page). Not a lunatic CCIE that’s afraid to fall asleep at night, worrying you’re muscle memory will forget the pieces of an IKEv2 Site-to-Site VPN? No problem! Take smaller bites at the topology to practice specific pockets of technology. Maybe you really want to see what happens when you accidentally cause a recursive routing loop in DMVPN (Ah yes; Mid-Chain Errors). Maybe you just want to practice VPNs or routing protocol authentication. Feel nervous about jumping into networking (although the blinking lights do seem enticing), LOAD IT UP and see how far you can get!! Although it may not cover 100% of the blueprint for CCIE Security V5, building and practicing this did give myself a considerable advantage trying to make everything work and communicate with the topology I’m providing here. One piece of advice for Lab candidates; If you don’t think there’s a way to connect two sites you’ll probably get that scenario on the lab, because you’re thinking “Do they REALLY need connectivity between X and Y?”.
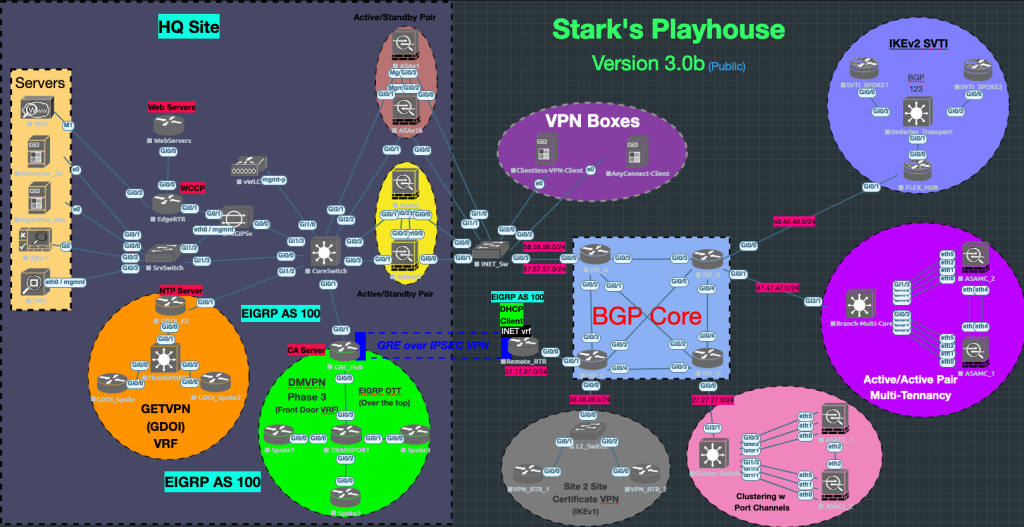
Here is the scenario I build out in my head, drawing from personal experience and osmosis from falling asleep on Cisco Press text books:
- An enterprise has started adding Secure Connectivity over it’s WAN and Internet connections.
- There are remote users who use AnyConnect, Clientless and GRE over IPSec connectivity.
- They also wanted to protect their “Web Servers” internally (simulated by HTTP pages on a router)
- The Enterprise has a tenant at another location and wants complete segmentation while leveraging existing equipment onsite
- etc… etc… etc…
I sprinkled in these Technologies while designing it, but FEEL FREE TO LAB AND MODIFY IT WITH WHAT YOU’RE COMFORTABLE WITH:
- EIGRP
- BGP
- OSPF (BGP’s IGP)
- Routing Protocol Authentication
- NTP
- Certificate Based VPN Connectivity
- AnyConnect using IKEv2
- Clientless SSL remote access
- IKEv2 SVTI
- Active/Standby ASAv Firewalls
- Active/Active ASA (old school 9.1) Firewalls
- Clustering for ASAs (old school 9.1) Firewalls
- Site to Site IKEv1 or IKEv2 Certificate Based VPN
- DMVPN phase 3 with a front door VRF
- GRE over IPSEC Connectivity from a home user’s router back to the GRE Hub
- GETVPN
- ISE
- Active Directory
- NGIPSv managed by FMC
- A Virtual WLC (for good measure)
- NAT
- Routing
- Switching
- Security
- Wireless
Genuine excitement, knowledge gaining and of course frustration from injecting your own faults (I do this a lot).
Feel like you’re unstoppable? Configure overlay VPNs between all of the sites and ping it out. Drop another windows box on the topology to see how AD works across a simulated IPSec WAN. Turn it up a notch, deploy 802.1x at your remote sites and push a CoA to authorize domain machines. Ok, let’s get a couple of boiler plate questions out of the way:
- No, I’m not quite interested in breaking NDA and losing my certs and street cred… So please, don’t ask.
- The lab is formatted for EVE-NG.
- I have included the Image Version names I was using to prep for my lab exam.
- I will not make the Images, BIN files, or any qcow2 files available, Sorry. My brother and I built the Windows boxes from scratch and the appliance images are mostly from Cisco’s site. Whatever I couldn’t grab from Cisco’s site, I was able to get from my Cisco Rep.
Download the Topology Here
Download the Image List Here
I hope that this topology is helpful to anyone studying, labbing or just in general to get how to connect two points on a network; even if they are several public hops away. Go learn something new, practice something familiar or just have fun!
- Stark out!


1 thought on “LAB 000 – Starting by Choice”
Comments are closed.